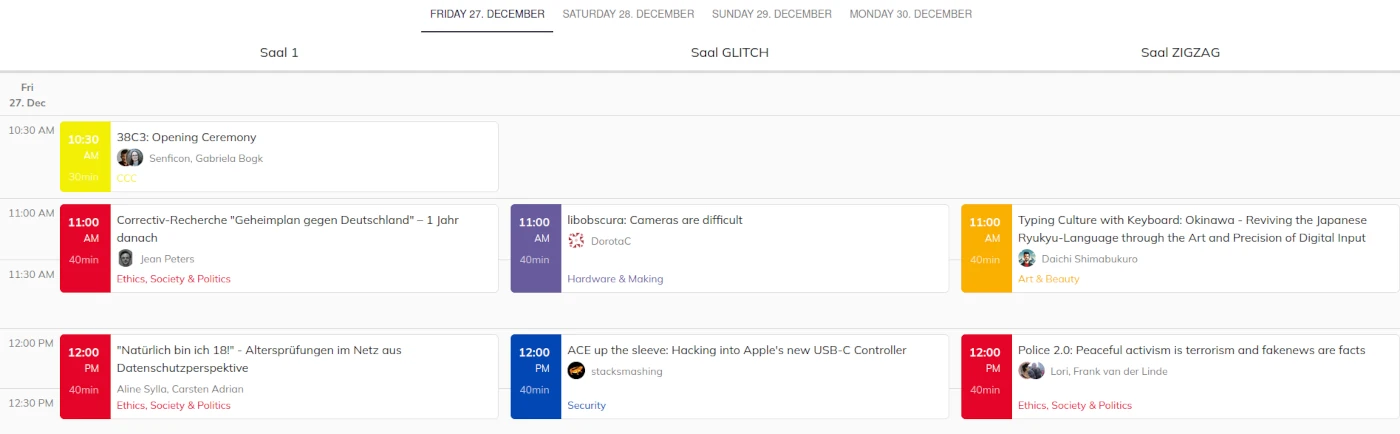
From halfnarp to schedule
Many thanks to everyone who filled out the halfnarp. Thanks to you and the many helping hands of the speaker desk and content teams, we can present the first version of the 38C3 schedule today!
The official program of the 38th Chaos Communication Congress comes up with 7 tracks containing 140 talks with 6625 minutes of program. There is definitely something for everyone! The 38C3 starts on December 27 at 10:30 with the Opening Ceremony and ends on December 30 at 18:00 with “Return to legal constructions”.
For those of you who have been counting by hand or even found the gaps in the program: …