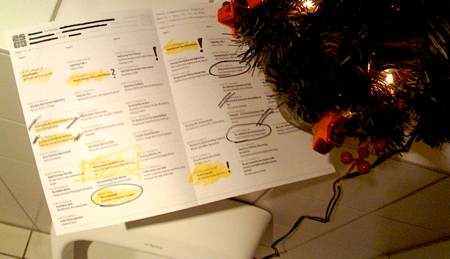
Let’s have a camping Fahrplan!
There are only a few days left and we are late but finally it is here: the Fahrplan for the Chaos Communication Camp 2015. Due to circumstances we had some lags, but finally we made it!
Please note this safety advices by going through the Fahrplan to pick your sessions:
- There is a new track: Failosophy. Read more about it in the Call for Papers.
- Mind the gap between 12:30 and 16:00. This is siesta-time where no lecture will be held in the lecture-tents. We decided to do so as this timeframe will be incredibly hot and we do not want to constipate you in tents while the heats is rushing over …

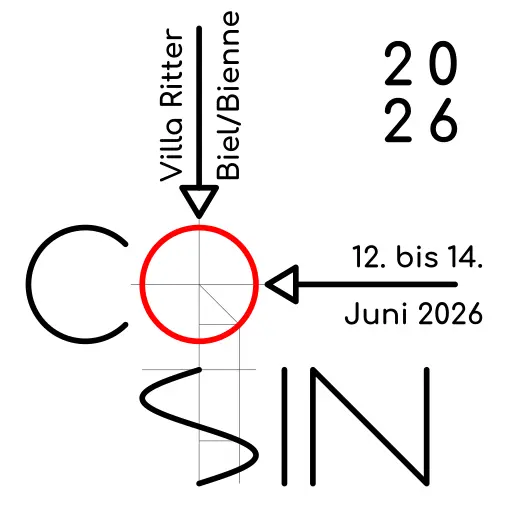
 Ab Donnerstag 23.6. bis Sonntag 26.6. findet in Karlsruhe die
Ab Donnerstag 23.6. bis Sonntag 26.6. findet in Karlsruhe die