Camp Schedule Published
Almost a week ago we published the Camp Fahrplan (schedule). Follow this link for more information.
Almost a week ago we published the Camp Fahrplan (schedule). Follow this link for more information.
 As a general attack against encryption software on a computer, the cold boot attack was presented at 25C3. To encrypt data on a PC, many programs store the encryption key in RAM. The key is usually derived from a password or loaded from the hard disk where it is protected by a password too. The key resists as least as long as the encryption operation take in RAM. For many applications like Full-Disk-Encryption or Email Signatures, it is convenient to keep the key permanently in RAM, once it has been loaded, so that the user doesn’t need to enter his password again and again.
As a general attack against encryption software on a computer, the cold boot attack was presented at 25C3. To encrypt data on a PC, many programs store the encryption key in RAM. The key is usually derived from a password or loaded from the hard disk where it is protected by a password too. The key resists as least as long as the encryption operation take in RAM. For many applications like Full-Disk-Encryption or Email Signatures, it is convenient to keep the key permanently in RAM, once it has been loaded, so that the user doesn’t need to enter his password again and again.
To protect the key …
SSL/TLS is the standard when it comes to securing HTTP traffic on the internet. The authenticity of a web server is usually secured using a X.509 certificate digitally signed by a trusted certification authority (CA). All major web browsers come with a list of CAs preinstalled they assume as trustworthy. Every website can be signed by any of these CAs, so no web browser would show a warning, if www.dod.gov would be signed by a Chinese certification authority or the Deutsche Telekom.
 To examine the usage of X.509 certificates for SSL/TLS, the EFF installed a SSL Observatory:
To examine the usage of X.509 certificates for SSL/TLS, the EFF installed a SSL Observatory:
The SSL …
 The new national id card Neuer Personalausweis (NPA) was one of the biggest IT projects in the German government in the last years. Compared to the old id card, the new id card is a RFID smart card, which can also be used on the internet to prove your identify to a remote party (Ebay, Paypal, or Amazon for example) and to sign binding contracts. For example, you can use the card to buy a new house or car, or open up a bank account or apply for a credit.
The new national id card Neuer Personalausweis (NPA) was one of the biggest IT projects in the German government in the last years. Compared to the old id card, the new id card is a RFID smart card, which can also be used on the internet to prove your identify to a remote party (Ebay, Paypal, or Amazon for example) and to sign binding contracts. For example, you can use the card to buy a new house or car, or open up a bank account or apply for a credit.
When using the card over the internet, the card is connected to a reader, which is connected to a (potentially insecure) PC, which is …
 Many applications, including closed source applications like malware or DRM-enabled multimedia players (you might consider them as malware too) use cryptography. When analyzing these applications, a first step is the identification and localization of the cryptographic building blocks (cryptographic primitives, for example AES, DES, RSA…) in the applications. When these blocks have been localized, the input and output of the cryptographic primitives and the key management can be observed and the application can be analyzed further. Fortunately, many cryptographic algorithms use special …
Many applications, including closed source applications like malware or DRM-enabled multimedia players (you might consider them as malware too) use cryptography. When analyzing these applications, a first step is the identification and localization of the cryptographic building blocks (cryptographic primitives, for example AES, DES, RSA…) in the applications. When these blocks have been localized, the input and output of the cryptographic primitives and the key management can be observed and the application can be analyzed further. Fortunately, many cryptographic algorithms use special …
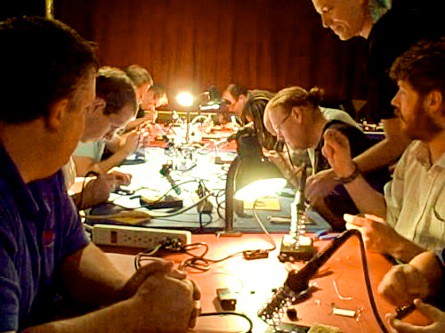
Hackers of all ages can (learn how to) make things at the Hardware Hacking Area of the 27c3!
The HHA is open to everyone and open the entire congress! Hackers of all ages and skill levels are welcome! Round-the-clock hands on workshops will be led by lots of experienced teachers like Mitch Altman, Jimmie P. Rodgers, fbz, Wim Vandeputte and…you!
Learn to solder, then help teach others! Make cool things with electronics, design and print 3D models on the Makerbot, break RFID, or give your own workshop on the projects you’ve been hacking on this year. Last year there was a Cantenna workshop, a …

Want four minutes on stage at the 27c3? You can have it! Registration is now open for the Lightning Talk sessions at the 27c3.
Taking place at 12:45 in Saal 3 on Days 2, 3 and 4, these fast paced sessions are perfect for pitching new software or hardware projects, exploits, creative pranks or strange ideas you need to share with the world.
Lightning talks are also good for getting publicity for your workshop at the 27c3, or for recruiting people to join in on things like a high calorie flash mob.
In order to maximize the available time, registrations will be granted to presenters who submit …
This past Sunday, we concluded the second and final Content Meeting for 27C3. We’ve looked at all 223 submissions for talks and presentations and selected what we feel are the best 98 of them. We’d like to thank all submitters for the many interesting proposals that lightened up our work.
One card for each talk that was accepted for 27C3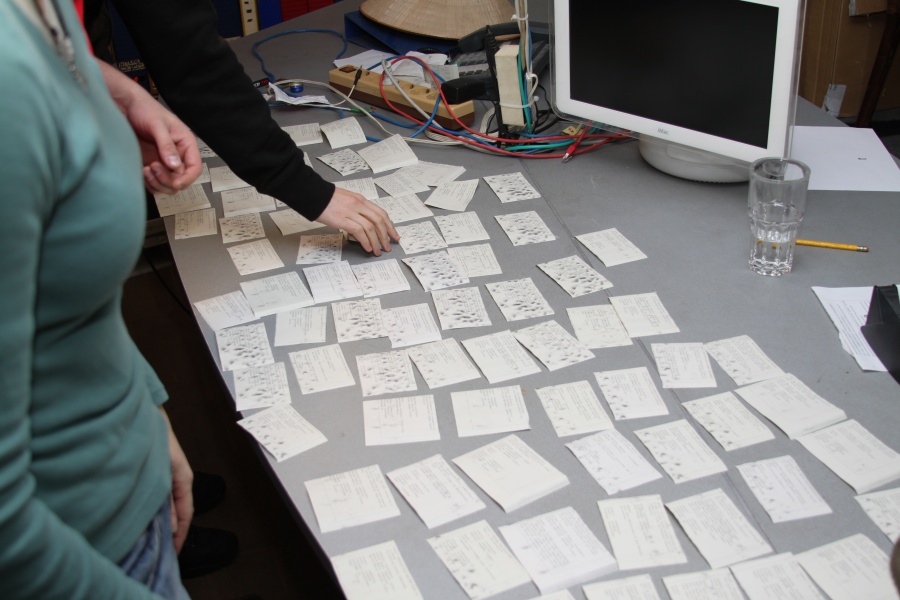
But now, the schedule for the 27th Chaos Communication Congress is mostly done. So today we …