Projects:Capture the Catcher
| Description | Objective: Find ways to exploit or crash an IMSI catcher. |
|---|---|
| Has website | https://opensource.srlabs.de/projects/snoopsnitch |
| Persons working on | |
| Self-organized sessions | create self-organized session |
| Tags | IMSI, IMSI catcher, GSM, Security |
| Other projects... ... further results | |
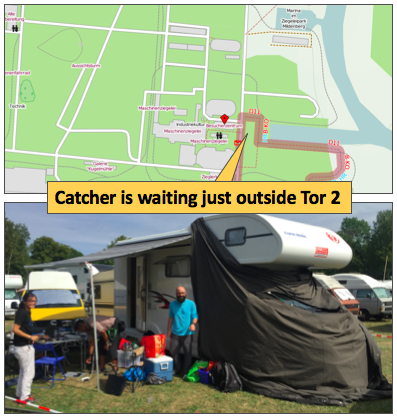
Setup. You will find a GSM network “crash_me” (MCC: 262, MNC: 23) at the camp, just outside Tor 2. This network behaves like an IMSI catcher. For example, it allows all users to connect, but does not conduct authentication and uses no encryption. The Catcher offers voice and SMS services, but does not actually connect your calls or deliver your SMS. The network uses a NanoBTS (which may well be used in real IMSI catchers) and the OpenBSC software (which is *not* used in any professional IMSI catchers).
Tools. Use whichever programmable radio you want to connect to the catcher. The simplest is an Osmocom_BB handset. The choice of exploitation technique is entirely yours, too. Fuzzing, protocol attacks, logic bombs, …
Results. Please post your crash vectors here. And please try not to use any of the vectors listed here again so to not interfere with the testing of others.
Discussion. We will review all results and chose the best vector at an ...
- IMSI catcher defense workshop:
- Day 3, 17:00, BER village
Happy hacking!
Results
| Attack vector | Found by |
| Ressource exhaustion through RACH bursts | Dieter Spaar, DeepSec 2009 |
| (post your vector here) | (post your name here) |