Generic settings
SSID: 39C3
EAP-TTLS:
Phase 1: EAP-TTLS
Phase 2: PAP
PEAP:
Phase 1: PEAP
Phase 2: MSCHAPv2 or EAP-MSCHAPv2 or PAP
CN = radius.c3noc.net
CA = ISRG Root X1
SHA256 Fingerprint = 06:81:9D:0D:21:47:91:DF:3A:31:4D:84:98:67:BF:9F:53:4E:F0:6D:F3:D4:B7:A0:6B:7D:8B:75:F9:E4:B6:7D
Make sure you check the certificate in order to know you are connecting to the correct network (you should check on both the CN and the CA).
Android
Connect to the 39C3 network using the following information:
- EAP method: TTLS (not TLS)
- Phase 2 authentication: MSCHAPv2
- CA certificate: Trust on first use (or install the certificate below)
- Domain: radius.c3noc.net
- Identity: 39C3
- Anonymous identity: leave blank
- Password: 39C3
Installing the root certificate
For best security, download the ISRG Root X1 certificate, and install it into your device’s Wi-Fi certificate store, giving it any name you like.
Linux, etc.
Network Manager
You can use the following config file:
Please note that some versions of NM are buggy and will only work with 802.1X using MSCHAPv2, or not at all. If that affects you, it may be easiest to use wpa_supplicant.
/etc/NetworkManager/system-connections/39C3:
Hint: chmod 600 this file to make the connection work.
[connection]
id=39C3
uuid=c80101e2-7b99-4511-846b-2388eb86a5ad
type=wifi
[wifi]
mode=infrastructure
ssid=39C3
[wifi-security]
auth-alg=open
key-mgmt=wpa-eap
[802-1x]
altsubject-matches=DNS:radius.c3noc.net
ca-cert=/etc/ssl/certs/ISRG_Root_X1.pem
eap=ttls;
identity=39C3
password=39C3
phase2-auth=pap
[ipv4]
method=auto
[ipv6]
method=auto
Network Manager via GNOME (graphical)
Similarly, you can also configure the WiFi through NetworkManager’s graphical user interface.
As for the certificate, it is usually preinstalled nowadays and in most distributions can be found in /etc/ssl/certs (file name: ISRG_Root_X1.pem). You need to select that manually. You can also use the cert bundle of your system - usually found at /etc/ssl/certs/ca-certificates.crt.
Otherwise, this is the configuration (the example shows the outboundonly username, as explained above, you can use any, as long as you use PAP as inner authentication mechanism):
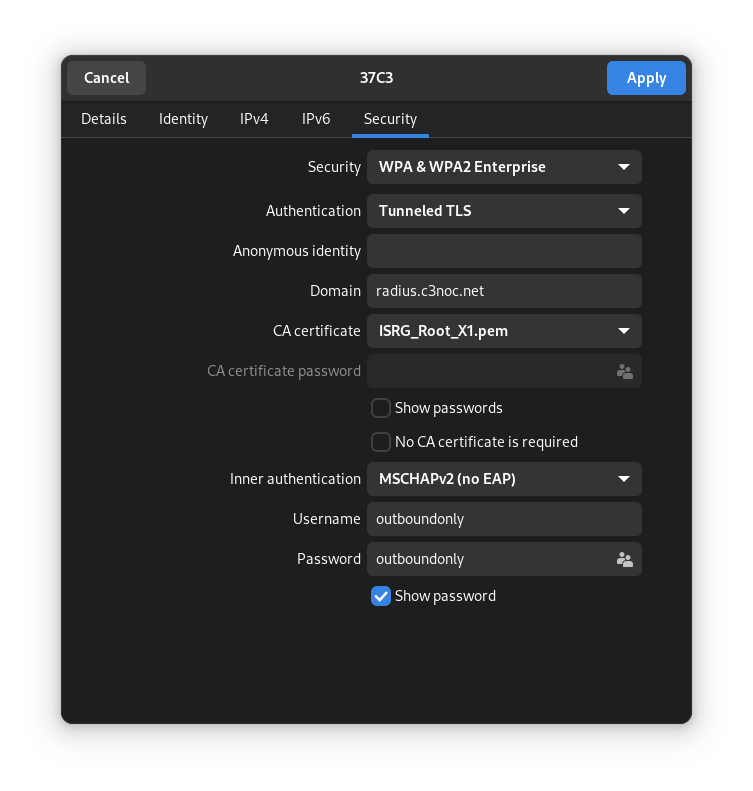
Security: WPA & WPA2 Enterprise
Authentication: Tunneled TLS
Anonymous identity: empty
Domain: radius.c3noc.net
CA certificate: ISRG_Root_X1.pem
CA certificate password disabled
“Show password” and “No CA certificate is required” unchecked
Inner authentication: MSCHAPv2 (no EAP)
Username: outboundonly
Password: outboundonly
WiCD
You need an additional crypto setting for WiCD. Put this file into /etc/wicd/encryption/templates/eap-ttls (Debian systems, might be different with other *nix flavours):
name = EAP-TTLS 39C3
author = Felicitus
require identity *Identity password *password
-----
ctrl_interface=/var/run/wpa_supplicant
network={
ssid="39C3"
scan_ssid=$_SCAN
identity="39C3"
password="39C3"
proto=WPA2
key_mgmt=WPA-EAP
group=CCMP
pairwise=CCMP
eap=TTLS
ca_cert="/etc/ssl/certs/ISRG_Root_X1.pem"
altsubject_match="DNS:radius.c3noc.net"
anonymous_identity="$_ANONYMOUS_IDENTITY"
phase2="auth=PAP"
#priority=2
}
Edit /etc/wicd/encryption/templates/active to include the eap-ttls config template. Restart the WiCD daemon, choose the proper encryption (EAP-TTLS 39C3) and enter a random username/password.
Jolla/connman
/var/lib/connman/39C3wifi.config:
[service_39C3]
Type=wifi
Name=39C3
EAP=ttls
Phase2=PAP
Identity=39C3
Passphrase=39C3
wpa_supplicant
This is the default option on Raspberry Pi OS. Edit /etc/wpa_supplicant/wpa_supplicant.conf and add the network:
network={
ssid="39C3"
key_mgmt=WPA-EAP
eap=TTLS
identity="39C3"
password="39C3"
# ca path on debian 7.x and raspberry pi OS, modify accordingly
ca_cert="/etc/ssl/certs/ISRG_Root_X1.pem"
altsubject_match="DNS:radius.c3noc.net"
phase2="auth=PAP"
}
Interfaces
As an alternative, you can specify the wpa_supplicant config options directly in /etc/network/interfaces:
iface wlan0 inet dhcp
wpa-ssid 39C3
wpa-identity 39C3
wpa-password 39C3
wpa-proto WPA2
wpa-key_mgmt WPA-EAP
wpa-group CCMP
wpa-pairwise CCMP
wpa-eap TTLS
wpa-phase2 "auth=PAP"
wpa-ca_cert "/etc/ssl/certs/ISRG_Root_X1.pem"
wpa-altsubject_match DNS:radius.c3noc.net
Netctl
Description='39C3 secure WPA2 802.1X config'
Interface=wls1
Connection=wireless
Security=wpa-configsection
IP=dhcp
ESSID=39C3
WPAConfigSection=(
'ssid="39C3"'
'proto=RSN WPA'
'key_mgmt=WPA-EAP'
'eap=TTLS'
'identity="39C3"'
'password="39C3"'
'ca_cert="/etc/ssl/certs/ISRG_Root_X1.pem"'
'altsubject_match="DNS:radius.c3noc.net"'
'phase2="auth=PAP"'
)
iwd
/var/lib/iwd/39C3.8021x:
[Security]
EAP-Method=PEAP
EAP-Identity=anonymous@39C3
EAP-PEAP-CACert=/etc/ssl/certs/ISRG_Root_X1.pem
EAP-PEAP-ServerDomainMask=radius.c3noc.net
EAP-PEAP-Phase2-Method=MSCHAPV2
EAP-PEAP-Phase2-Identity=39C3
EAP-PEAP-Phase2-Password=39C3
[Settings]
AutoConnect=true
Depending on your OS, the cert is in a different location. The path in Fedora 43 has been reported as:
/etc/pki/ca-trust/extracted/pem/directory-hash/ISRG_Root_X1.pem
NixOS
NetworkManager
networking.networkmanager.ensureProfiles.profiles = {
"39C3" = {
connection = {
id = "39C3";
type = "wifi";
};
wifi = {
mode = "infrastructure";
ssid = "39C3";
};
wifi-security = {
auth-alg = "open";
key-mgmt = "wpa-eap";
};
"802-1x" = {
anonymous-identity = "39C3";
eap = "ttls;";
identity = "39C3";
password = "39C3";
phase2-auth = "pap";
altsubject-matches = "DNS:radius.c3noc.net";
ca-cert = "${builtins.fetchurl {
url = "https://letsencrypt.org/certs/isrgrootx1.pem";
sha256 = "sha256:1la36n2f31j9s03v847ig6ny9lr875q3g7smnq33dcsmf2i5gd92";
}}";
};
ipv4 = {
method = "auto";
};
ipv6 = {
addr-gen-mode = "default";
method = "auto";
};
};
};
wpa_supplicant
networking.wireless.networks."39C3".auth = ''
key_mgmt=WPA-EAP
eap=TTLS
identity="39C3"
password="39C3"
ca_cert="${builtins.fetchurl {
url = "https://letsencrypt.org/certs/isrgrootx1.pem";
sha256 = "sha256:1la36n2f31j9s03v847ig6ny9lr875q3g7smnq33dcsmf2i5gd92";
}}"
altsubject_match="DNS:radius.c3noc.net"
phase2="auth=PAP"
'';
Apple macOS
To enable the most secure WiFi configuration on macOS:
- Download this mobileconfig file and double-click on it. You’ll get an unhelpful notification.
- Open Settings and search for the “Profiles” pane.
- Click the “+” button and select the mobileconfig file.
- After you’ve finished the install, your computer should automatically connect to the 39C3 WiFi.
Apple iOS
To enable the most secure WiFi configuration on iOS, open this mobileconfig file in Safari. After the file is installed, your device should automatically connect to the 39C3 WiFi.
Windows
Windows users (and other clients using MSCHAPv2) should use a fixed username and password. You can use “39C3/39C3” or “guest/guest” as username/password.
Import one of these profiles for the most secure WiFi settings for Windows:
- 39C3 (2.4GHz+5GHz)
To import and connect follow these steps:
- Open a command prompt and execute: netsh wlan add profile filename=39C3.xml
- Connect to the 39C3 network; use “39C3/39C3” as the username/password when prompted. Alternatively, use “outboundonly/outboundonly” as the username/password to enable inbound traffic firewalling.