23C3 - 1.5
23rd Chaos Communication Congress
Who can you trust?
| Speakers | |
|---|---|

|
Dan Kaminsky |
| Schedule | |
|---|---|
| Day | 2 |
| Room | Saal 1 |
| Start time | 21:45 |
| Duration | 01:00 |
| Info | |
| ID | 1713 |
| Event type | Lecture |
| Track | Hacking |
| Language | English |
| Feedback | |
|---|---|
|
Did you attend this event? Give Feedback |
Black Ops 2006 Viz Edition
Pixel Fuzzing and the Bioinformatic Bindiff
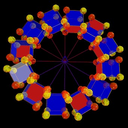
Tools for visualizing the genome can be repurposed to visualize code. Visualized code can be used as a map for fuzzing efforts, change identification, and showing your mom what you do for a living. I'm going to demonstrate a series of tools that brings a new, half-automated, half-visually driven approach to data manipulation and destruction.
The human genome is a mess. Whats on your hard drive is significantly less so. So what happens when you take a visual pattern representation method -- Dotplots -- built for ACTG and throw it at 0x42424242? Exceedingly ornate imagery erupts. Now, what happens when you start fuzzing the data you're visualizing? Your image gets fuzzy, based on precisely what faults your injecting into the data. This Black Ops talk is going to bounce repeatedly between the domain of information representation and the domain of information corruption. I'm going to discuss the use of a linear time context free grammar generator to create a higher-order file fuzzer, and we're going to visualize the output of that fuzzer in realtime. I'm also going to show off other patterned signals that can potentially be comprehended better through graphical summarization, like execution flow traces. I'll also show a rather unexpected result -- that comparing two different versions of the same file visually makes for exceedingly rapid change detection. Finally, I'll probably find some way to squeeze in the concept of cryptomnemonics; this is where a bit sequence 0x123AFFE2 gets mapped to a series of names ("John and Leia Lindner") that encapsulates arbitrary entropy in human recognizable values.
New tools will absolutely be released at this talk.
